LinkedIn Is Searching Your Computer
The investigation LinkedIn doesn't want you to read.
I am about to cover all the nefarious ways LinkedIn operates by focusing on a recent investigation that blows the lid on some serious espionage.
But if you take one thing away, understand this: associating LinkedIn only as a professional platform is propaganda through the use of euphemisms and framing. You can see it in their own tagline: “Connect professionals to boost productivity and success.” It seems innocent at first glance, but LinkedIn isn’t clear on how they were going to connect professionals and whose success and productivity it’s for. Today I’ll dive into how they really connect professionals and whose success and productivity this platform actually serves using this new investigation done by Fairlinked.
Here’s what you’re going to learn in this post:
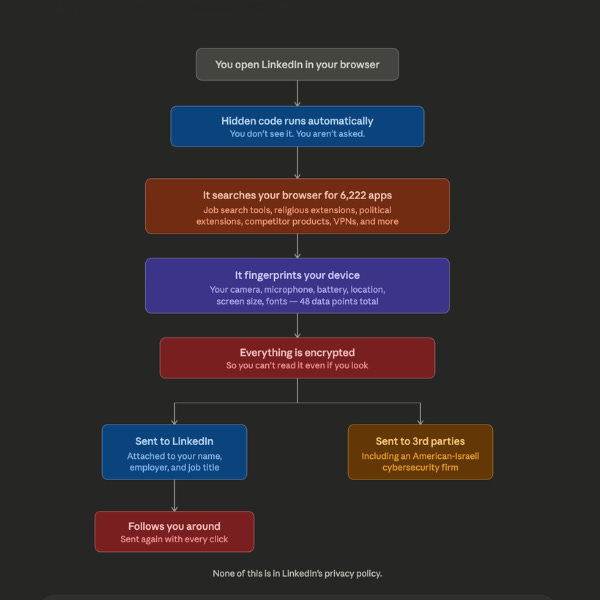
Every time you visit LinkedIn on Chrome, Edge, Brave, or Arc, hidden code may be scanning your computer for installed software as well as sending the results back to LinkedIn’s servers. You did not consent to this, you did not receive a notification, nor was this mentioned in their privacy policy. If you’ve ever used a job search extension while quietly looking for a new role, LinkedIn may know and tie this data to your real name and your current employer. If you use a religious, political, or accessibility extension, LinkedIn may have that too. The scan covers 6,222 software products with a combined user base of 405 million people, and it’s growing by roughly 12 new extensions per day. LinkedIn is also feeding your data to third-party companies you’ve never heard of, including an American-Israeli cybersecurity firm, through invisible tracking elements hidden off-screen on the page. Moreover, they built this system during the exact period when European regulators ordered them to open up to competition. So, instead of complying, LinkedIn expanded surveillance of the very tools the law was designed to protect. Crazy!
TLDR: My observations from last year around LinkedIn’s capability to surveil is no longer speculation. This is now documented in LinkedIn’s own source code, and you can verify it yourself. I’ll show you how.
But first, let me start with where I left off in December. Here are the posts if you wish to re-read:
Part 1: LinkedIn is a National Security Asset
Part 2: Reid Hoffman and Peter Theil Come from the Same Machine
In the above posts, I identified that LinkedIn has the capability to be a national security asset. I identified that Reid Hoffman was touched by the government long before he announced the official partnership between LinkedIn and the Department of Defense. I told you not to ignore Microsoft’s acquisition of LinkedIn, which requires us to consider Bill Gates and Microsoft’s partnerships, connections, and tech infrastructure. I told you about LinkedIn’s integration with Palantir. I told you Hoffman was someone to be critical about no matter how wide and jolly his smiles are.
My worldview, through my own pattern recognition, is that most of these tech players we are expected to praise and glaze are not bootstrapping their ideas. They have help, or they are intercepted by the government during their origin story and Hoffman is no exception. As I walked through with you lastt year, he and Peter Thiel are nearly the same age, attended Stanford at similar times, and their educations complemented each other. These two men are connected because Thiel learned how to build foolproof monopolies through his mimetic theory discipline, and Hoffman became the ethics guy who took classes with CIA-connected professors. These two men still have a relationship today. No matter how much are publicly distancing themselves as Hoffman panders to Democrats and Theil to Repbulicans. And Hoffman has correspondence with Epstein. Although, as I have mentioned prior, none of the declassified files are incriminating, his timeline of admitting that association isn’t consistent through his public statements, and the times he says he was with Epstein are not congruent across his stories. Where there are little lies, we cannot assume there are no big lies. If you have kids, I’m sure you can relate.
So last year I told you LinkedIn was a surveillance platform and now I have the receipts to show how that surveillance actually works; both in how it’s used on us domestically and what it enables at scale. A European association, called Fairlinked, published an investigation in early 2026 documenting how LinkedIn secretly scans your computer every time you visit the site. They’ve since filed legal proceedings under the EU’s Digital Markets Act. Their investigation includes a downloadable evidence pack, and every claim can be independently verified by opening LinkedIn’s own source code in your browser.
Here is a diagram I created with Claude, without the tech jargon, to summarize what I am about to walk you through:
One more thing before I get into the findings because I know a lot of you wonder about my position on these things as a public figure in the career space. LinkedIn is still the king of networking; so therefore, I choose to still use the platform today specifically for business purposes. Additionally, I have a business relationship with them. At the same time, I’m not afraid of the potential to lose that relationship over telling the truth. And if they do retaliate, that will just further prove my point.
Finally, let’s get into what Fairlinked found!
The Scan
Every time you visit linkedin.com on a Chrome-based browser (which also includes Edge, Brave, Arc, and Opera), LinkedIn serves you a JavaScript bundle containing hidden code that scans your computer for installed browser extensions.
Two detection systems run simultaneously. The first brute-forces a list of 6,222 known extensions by firing thousands of requests against your browser to check whether each one is installed. The second walks the entire structure of the webpage looking for traces of any extension activity, catching extensions that might not be on the list.
As I mentioned in the beginning of this post, there’s no consent dialogue nor informed consent.
The system was built to be invisible. It can wait until your browser is idle before executing, so you never see a performance hit. It can stagger the requests over time so they don’t show up as a suspicious burst in your network monitor. Failed checks are silently discarded with no errors or console warnings. And the results are encrypted before transmission, so even if you inspect the network request, you can’t read what was sent.
One important caveat: LinkedIn controls this system through internal feature flags on their A/B testing platform. This means the code is served to all Chrome-based visitors, but LinkedIn can gate who actually gets scanned. The fact that they’re A/B testing a surveillance system is its own kind of disturbing because it means they are actively experimenting with how to scan you more effectively.
What the Scan Reveals About You
The scan list entails an intentionally curated collection of browser extensions. It includes extensions that reveal some of the most sensitive categories of personal information that exist under law. Here are the buckets they are creating:
Religious beliefs. Extensions like PordaAI, which blurs haram content, and Deen Shield, which blocks haram sites, are on the list. If the scan runs on you and you have one of these installed, LinkedIn receives that data tied to your session and can make the assumption that the user is Islamic.
Political opinions. Extensions like “Anti-Zionist Tag,” “Anti-woke,” and “No more Musk” are on the list to gather political learnings about its users.
Disability and neurodivergence. Extensions built for neurodivergent users, like “simplify,” are on the list. This is creepy to realize LinkedIn is gathering data that can make assumptions on who is neurodivergent or not.
Job-seeking activity. This is the one that should make your stomach drop if you’re reading this on a work computer. 509 job search extensions are on the scan list. If you’ve been secretly looking for a new role while still at a current job, LinkedIn may have detected that. So the very platform where your current employer’s recruiters, HR team, and managers are active is gathering a list of who is looking for new jobs before having the ability to land a new role and alert their current employer.
Now here’s what makes this different from any other data breach you’ve read about. LinkedIn is not an anonymous forum like Reddit. It’s not even like Instagram, where you can shitpost once a year and still get value from the app. Your relationship with LinkedIn is different, as it only works if you feed it the truth, like your real name, current employer, actual job title, career goals, professional relationships. If you don’t keep that information current and honest, you can’t network, get recruited, nor use the platform as intended. That’s the deal you make when you sign up. Compare that to Instagram, where the most valuable thing you’re giving up is where you went last July for your cousin’s wedding. LinkedIn has everything someone would need to reverse engineer your economic opportunity, your earning potential, your next career move, and your livelihood. And that’s what makes it such a powerful asset as every data point the scan collects is attached to all of that.
The investigation confirms these extensions are hardcoded in LinkedIn’s production JavaScript. What it doesn’t independently prove is that LinkedIn is actively cross-referencing scan results with your profile data to build individual dossiers. But as Fairlinked points out, the aggregation is trivial as LinkedIn already has both data sets in the same system.
What the Scan Reveals About Your Company
This is now where it scales from just creepy to strategic.
Because LinkedIn knows where every user works, individual scan results can aggregate into profiles of entire organizations. Therefore, the technical capability is confirmed. Whether LinkedIn actively builds these organizational profiles is alleged by the investigation, not proven with internal documents. But the architecture makes this claim almost automatic.
If employees across your company have Salesforce extensions installed, LinkedIn can infer you’re a Salesforce customer. If 30% of your team is running job search extensions, LinkedIn can infer you have a retention problem. If some of your employees have security tools installed and others don’t, LinkedIn can map your company’s security posture. If political or religious extensions cluster among your workforce, LinkedIn has a read on your internal culture.
None of this requires any sophisticated analysis. It’s just extension data plus employer data and LinkedIn has both. And this doesn’t only affect you as it affects your employer too.
I can feel some of you already shifting to: who cares about my employer? And also….Ms. AntiWork, why do you all of the sudden care about employer safety?
Because private companies are an extension of the government. I’ve discussed this with you before, but the Department of Def - I mean War, sorry I can’t keep track - works directly with private companies, especially Fortune 500s. Most people have come to accept that, and many of you may even work on government contracts at your private companies and find it innovative. Great. But did you know that the work you do for the government through a private company cannot be accessed through FOIA requests by the public? Because the projects are owned by the private company, not the government. Why would the government want to route so much of their work through a structure that isn’t subject to public transparency? Makes you wonder….
Anyways, I digress. While I do not put employers’ interests over employees’ interests, I am still concerned with corporate espionage. Let’s get into how that works!
Corporate Espionage
Now, this is the part that moves from privacy violation into something that looks like competitive intelligence at scale.
LinkedIn scans for 209 sales and prospecting tools , including Apollo, Lusha, and ZoomInfo, that directly compete with LinkedIn’s own Sales Navigator product, which generates roughly a billion dollars a year in revenue. Huba-huba!
By detecting which users at which companies have competitor tools installed, LinkedIn can effectively compile the customer lists of thousands of software companies without asking or paying those companies or those companies knowing about it.
And this is no longer a theory or a hunch because Fairlinked states that LinkedIn has already sent enforcement threats to users of third-party tools, using data obtained through this covert scanning to identify its targets. The mechanism for how they identify these users is confirmed in the code. Just the scale at which they act on it is what the investigation alleges.
To put this in perspective: if an employee at any of these companies walked out with a USB drive containing a competitor’s customer list, they’d face criminal prosecution. LinkedIn does it to 6,222 companies simultaneously, continuously, and at scale. All Hail, our Democratic angel, Reid Hoffman!
Government Exposure
The scan doesn’t distinguish between a marketing manager at a startup and a cybersecurity analyst at a European defense ministry as the same code runs on both.
Government employees, military personnel, intelligence professionals, regulators, and elected officials all use LinkedIn with their real names and institutional affiliations. The scan code runs on all Chrome-based visitors, subject to whatever feature flags LinkedIn has enabled.
What this structurally exposes: the security tools (or lack thereof) that government employees use. Whether intelligence or military personnel are quietly job hunting. Technology procurement choices that may be sensitive or classified. And, in a particularly uncomfortable irony, the EU regulators responsible for enforcing the Digital Markets Act against LinkedIn are almost certainly on LinkedIn themselves and subject to this scanning.
This is a structural risk of the system’s design. The investigation does not document a specific case where LinkedIn exploited government employee data, but the exposure is inherent in the architecture. So LinkedIn could go exploit our own government or another nation’s government. Which goes back to my December claims: LinkedIn IS apart of our military-industrial complex.
Where the Data Goes
The scan results doesn’t stay within LinkedIn, as the system feeds data to at least 3 external services. This is all confirmed in the production code:
A hidden iframe, zero pixels wide, positioned off-screen, loads from HUMAN Security (formerly PerimeterX), an American-Israeli cybersecurity firm. It sets cookies on your browser without your knowledge.
Side note: American companies will use Israeli tech firms to bypass American regulations and laws. If a company wants to perform a cybersecurity task that would be considered illegal domestically in the US, there are Israeli partners that will perform the task on their behalf. I cannot share my source for this information to protect both my information gathering and the person who shared this.
Now pan out and think about how many tech companies are owned by, operated by, or in partnership with Israeli citizens or how many American citizens who run major monopolies hold dual citizenship with Israel, like Larry Fink at BlackRock and Larry Ellison at Oracle. This extends into social meda, traditional media companies, banking systems, our nations assets management and beyond.
I want to be precise about what I’m saying here: this is not a point about Jewish people, religion, or sovereignty. This is a critique of a specific cybersecurity pipeline between two nations and whether that pipeline serves the interests of regular Americans or not. The only reason I bring this up is because one of the third-party companies I mentioned above that LinkedIn is funneling your data to like HUMAN Security, formerly PerimeterX. And since, this firm is an American-Israeli cybersecurity firm, that detail matters in this context.
A separate fingerprinting script loads from a LinkedIn subdomain, passing your session cookie.
Google reCAPTCHA v3 Enterprise then executes silently on every page load.
Then, all of these integrations are controlled by feature flags within LinkedIn. When enabled, they run without any disclosure to the user. What’s not fully clear from this investigations findings, is exactly what data each third party receives from the extension scan specifically versus the broader fingerprinting system, but they’re all part of the same architecture.
It’s More Than Extensions
The extension scan is actually one piece of a much larger fingerprinting system LinkedIn calls APFC and this system collects 48 distinct characteristics from your browser every time you visit.
APFC collects:
Your IP address via WebRTC.
Your connected cameras, microphones, and speakers.
Your CPU cores and RAM.
Your battery level and charging status.
Your installed fonts.
Your canvas fingerprint.
Your WebGL data.
Your network speed and connection type.
Your timezone.
Whether you’re in incognito mode.
One detail that says everything about the mentality behind this system is LinkedIn records your Do Not Track browser setting. Then, it explicitly excludes that setting from the fingerprint hash and they note that you asked not to be tracked. Then, they track you. LOL, okay…coolsies.
This fingerprint doesn’t just get sent to you once. It’s encrypted and injected as an HTTP header into every API request you make during your session. So, every action you take on LinkedIn like every profile view, search, message, then carries your fingerprint with it.
The Scale
The scan list has grown exponentially:
2017: 38 extensions
2024: ~461
May 2025: ~1,000
December 2025: 5,459
February 2026: 6,167
That’s roughly 12 new extensions added per day which proves, the system is actively maintained and expanding. The extensions on the current list have a combined user base of approximately 405 million people.
The timing of this matters as well. The explosive growth in the scan list from 461 to over 6,000 directly tracks the period when LinkedIn was supposed to be complying with the EU’s Digital Markets Act, which ordered LinkedIn to open its platform to third-party tools.
EU Compliance Theater
In 2023, the EU designated LinkedIn as a gatekeeper under the Digital Markets Act and ordered LinkedIn to provide access for third-party tools.
LinkedIn’s response was publishing two restricted APIs that together handle approximately 0.07 calls per second. Meanwhile, LinkedIn already operates an internal API called Voyager that powers every LinkedIn web and mobile product at 163,000 calls per second.
In Microsoft’s 249-page compliance report to the European Commission, the word “API” appears 533 times. “Voyager” appears zero times.
While presenting these token APIs as compliance, LinkedIn expanded its surveillance of the exact tools the regulation was designed to protect. The EU told LinkedIn to let third-party tools in, then LinkedIn built a system to find and punish every user of those tools.
In January 2026, legal proceedings were filed against LinkedIn in Munich by Teamfluence, an Estonian software company, represented by the same law firm that secured the first successful DMA-based private enforcement action (that case was against Google).
What This Means
I wrote in December that LinkedIn operates as a surveillance platform with structural insulation from accountability, and BrowserGate now shows us the technical evidence for that claim.
Please don’t let them get away by telling you this was a bug, or an isolated incident, and this is not from one rogue engineer. Do not let them do a Cambridge Analytica Part 2 where they get off by doing damage control by blaming employees. This is a system that was deliberately designed to be invisible, that has been actively maintained and expanded over years, that is controlled by A/B testing flags so LinkedIn can optimize how it surveils you, and that has grown 10x during the exact period when regulators told LinkedIn to open up.
Before we end with some takeways for you moving forward, remember me mentioning LinkedIn’s tagline? “Connect professionals to boost productivity and success.” I told you at the top that LinkedIn was never clear on how they were going to connect professionals and for whose success and productivity it’s for. Now you have the answer.
They connect professionals by scanning their browsers, mapping their tools, their beliefs, their job-seeking activity, and their employer’s entire technology stack. Then they trasmitt all of it, encrypted, to their own servers and to third-party companies, companies which you’ve never consented to share data with.
And whose success and productivity does the platform serve? Not yours. It serves LinkedIn’s billion-dollar sales product by identifying and suppressing competitor tools. It serves Microsoft’s government contracts by sitting on top of the largest verified professional directory in the world. And it serves the intelligence value of a platform that knows the real name, real employer, and real career intentions of over a billion people. That’s the full picture and whose productivity LinkedIn is for.
If you use LinkedIn, and most of us don’t have a real choice, here’s what you can do:
Check what browser extensions you have installed and understand what they reveal about you
Read Fairlinked’s full investigation at browsergate.eu
If you’re in the EU, the investigation includes guidance on filing complaints
Share this with anyone who still thinks LinkedIn is just a harmless job board
I’ll be covering this story as it develops, especially as the Munich legal proceedings move forward. If you’re a founder, a tool maker, or someone who has received enforcement threats from LinkedIn, I want to hear from you!
This post draws on the BrowserGate investigation published by Fairlinked e.V. (browsergate.eu), a European association of commercial LinkedIn users. All technical claims are documented in their evidence pack and can be independently verified by examining LinkedIn’s production JavaScript. For my previous coverage of LinkedIn as a national security asset, read my December 2025 post [here].